Why modern authentication feels confusing—and why architects can no longer ignore it
If you work in cloud, DevOps, platform engineering, or AI today, you’ve probably heard advice like this:
“Use OAuth.”
“No, use OIDC.”
“Use mTLS for service-to-service.”
“Use SAML for enterprise SSO.”
“Use Workload Identity Federation for CI/CD.”
“Propagate user identity for AI agents.”
At some point, most engineers stop nodding confidently… and start silently Googling.
Because let’s be honest:
Modern authentication is one of the most misunderstood topics in engineering.
Not because it is inherently difficult. But because the world changed.
A decade ago, authentication mostly meant:
- Username
- Password
- Login screen
Today, identity flows through:
- Humans logging into UIs
- APIs calling APIs
- Microservices communicating internally
- CI/CD pipelines deploying infrastructure
- Cloud workloads accessing managed services
- AI agents invoking tools autonomously
Authentication is no longer just “login.”
- It is architecture.
- It is security.
- It is trust.
And increasingly it is the difference between a resilient platform and a security incident.
First Principles: Start Simple
At the heart of all this complexity are only two concepts.
Authentication (AuthN)
Authentication answers:
Who are you?
Examples:
- A user logging into an application
- A service identifying itself to another service
- A pipeline proving its identity to a cloud provider
Authorization (AuthZ)
Authorization answers:
What are you allowed to do?
Examples:
- Can this user view reports?
- Can this service trigger automation?
- Can this pipeline deploy infrastructure?
Everything else—OAuth, OIDC, JWT, SAML, mTLS—is simply a mechanism built around these two ideas.
Why Authentication Feels So Confusing
Because modern systems are running multiple identity conversations at the same time.
A single workflow may involve:
- A user logging into a portal
- The portal calling APIs
- APIs talking to internal services
- Services accessing cloud resources
- Pipelines deploying updates
- AI agents triggering actions
Each interaction may use a different trust model.
That’s where confusion starts.
The trick is to stop memorizing terms and start understanding where identity is flowing.
1. Human → UI Authentication
This is traditional login.
A user opens an application and signs in.
Typical mechanisms:
- OIDC
- SAML
- Session Cookies
Example Flow: Enterprise Portal Login
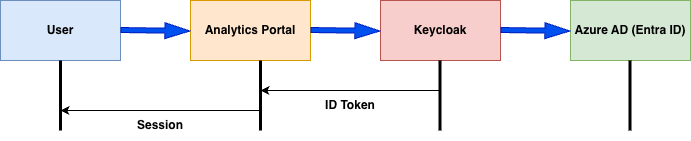
What happens?
- User opens the portal
- Portal redirects to Identity Provider
- Identity Provider authenticates user
- Token/session returned
- User gains access
This is interactive authentication.
The most familiar kind.
2. API → API Authentication
Applications talk to applications.
Common mechanisms:
- OAuth2 Access Tokens
- JWT Bearer Tokens
- API Keys
Example Flow: Third-Party API Access
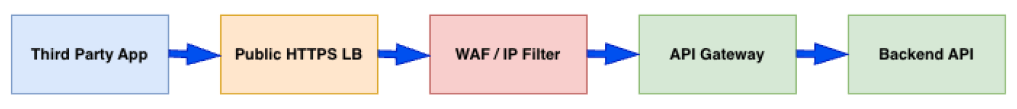
Authentication proves identity.
Authorization checks scopes and permissions.
This is where OAuth2 typically shines.
3. Service → Service Authentication
Now we move into Zero Trust territory.
Services inside Kubernetes or microservice platforms need authentication too.
Common mechanisms:
- mTLS
- Service Accounts
- OAuth Client Credentials
- Workload Identity
Example Flow: Internal Service Communication
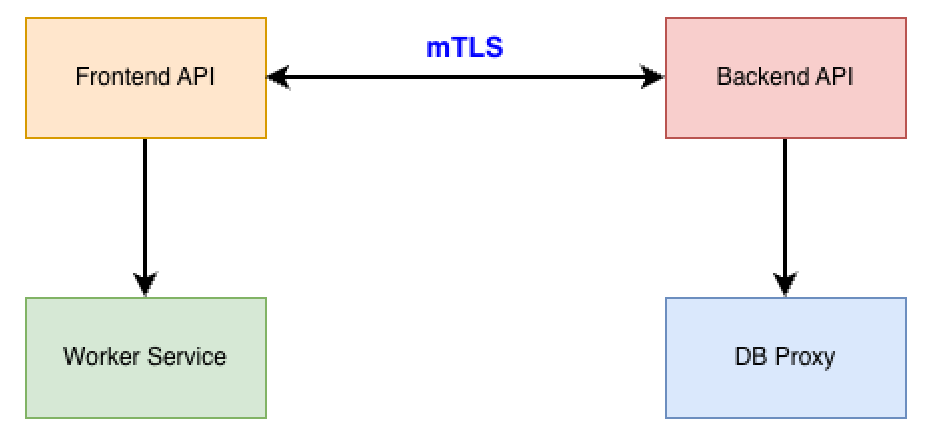
mTLS ensures:
- Server is trusted
- Client is trusted
4. Pipeline → Cloud Authentication
CI/CD pipelines are identities too.
And if compromised, they can be dangerous.
Old model:
Long-lived secrets.
Modern model:
Federated identity.
Example Flow: GitHub Actions Deploying to Cloud
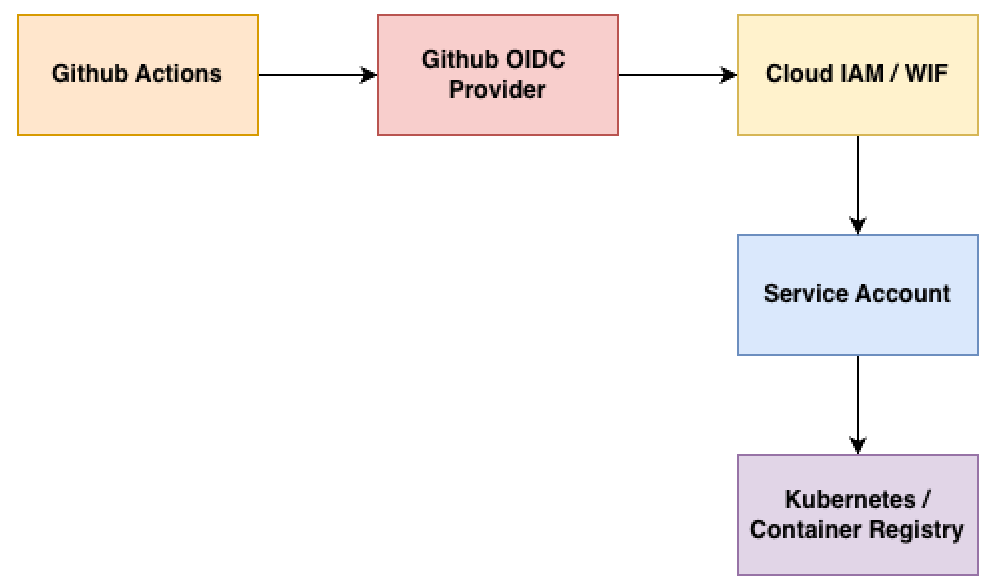
Benefits:
- No static credentials
- Temporary access
- Claim-based trust
One of the biggest improvements in modern platform security.
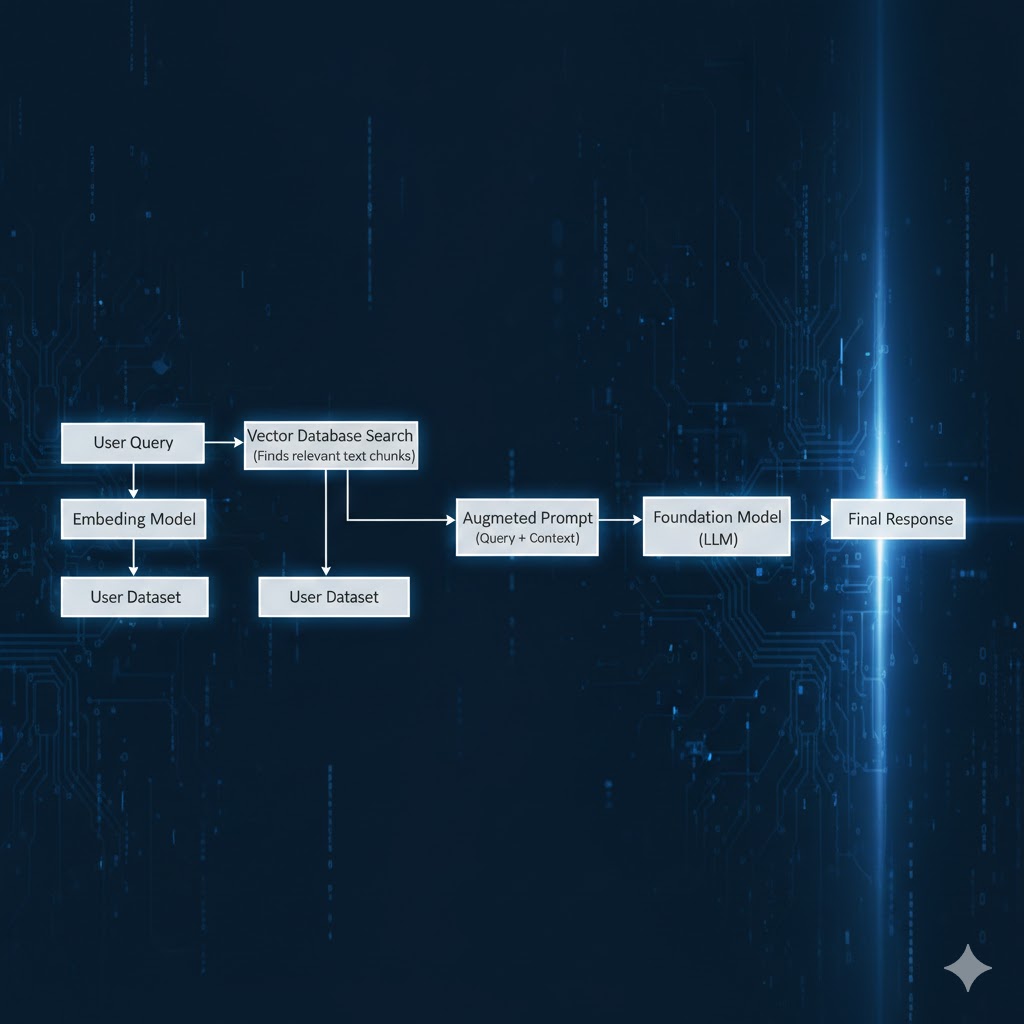
5. Agent → Tool Authentication
This is the newest challenge.
AI agents don’t just answer questions.
They act.
They may:
- Query metadata
- Call APIs
- Trigger workflows
- Create tickets
- Send alerts
- Invoke LLM endpoints
Example Flow: Agentic Workflow Authentication
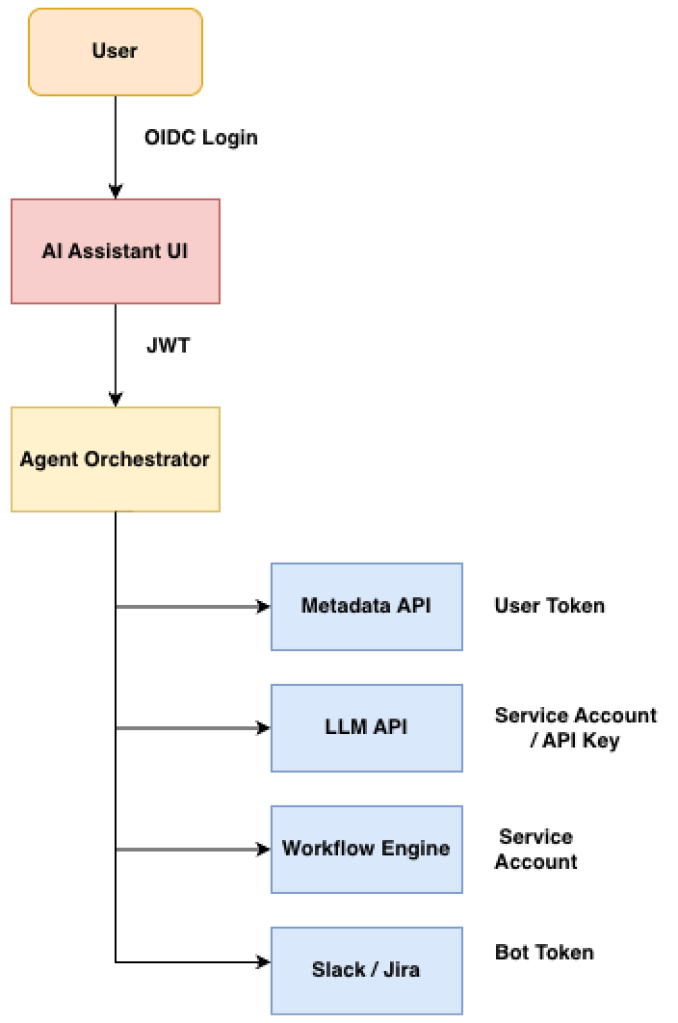
One workflow.
Multiple identities.
This is where modern architecture gets interesting.
And risky.
The big question becomes:
Whose identity is the agent using?
- The user’s?
- Its own?
- A delegated role?
This is the next frontier in authentication design.
The Terms People Mix Up
Quick refresher:
- OAuth2 → Authorization framework
- OIDC → Authentication layer based on OAuth2
- JWT → Token format carrying claims
- SAML → Older enterprise SSO protocol
- mTLS → Mutual certificate-based authentication
- IdP → Identity Provider
One common misunderstanding:
JWT is not a protocol.
It is just a token format.
A Practical Decision Framework
Whenever choosing authentication, ask:
1. Is the caller human or machine?
Human → OIDC / SAML
Machine → mTLS / OAuth / Service Identity
2. Is the interaction interactive or automated?
Interactive → browser login
Automated → tokens / certificates / federation
3. Is the call inside or outside trust boundary?
Inside → mTLS / Workload Identity
Outside → OAuth / OIDC / API Gateway
These three questions simplify most decisions.
Final Thoughts
Authentication feels confusing because systems evolved faster than our mental models.
We are no longer building simple applications.
We are building ecosystems of:
- Users
- Services
- APIs
- Pipelines
- Agents
All communicating across trust boundaries.
And in the age of APIs, agents, and Zero Trust…
Trust is no longer assumed. It must be designed.


Leave a comment